What’s Your Porn Star Name? A Cybercriminal Wants to Know

How Personally Identifiable Information is Being Harvested, and Why You Are Helping Them Do It.
The information you didn’t know you were giving away
Here is a question: When did you last stop to think about how much of yourself you have handed over to the internet, for free, with a smile on your face? Not through a data breach. Not because a hacker broke through some corporate firewall at three in the morning. But voluntarily. Cheerfully. Sometimes with a laughing emoji attached?
Personally Identifiable Information (PII) refers to any data that can be used to identify, locate, or single out a specific person. The term emerged from United States privacy discussions in the 1970s and has since become the cornerstone of global cybersecurity frameworks, data protection legislation, and digital identity systems.
There are two categories that are used to define PII, direct information, which can identify you on its own (full name, national ID number, passport, bank account details, biometric data), and indirect information, which cannot identify you alone but becomes dangerous when combined with other sources, like your job title, your employer, your browsing patterns, your IP address, your hobbies, and yes, even the street you grew up on.
That last one should trigger your memory, because if you have ever taken one of those social media quizzes, “What is your porn star name?” or “Create your superhero alias!”, you may have handed a cybercriminal two answers to your digital security questions without them having to ask.
Your Profile is a Product, and Someone is Selling it.
Let us start with what is happening at scale, because the numbers are staggering. In November 2025, cybersecurity researchers uncovered an unprotected MongoDB database containing 4.3 billion records, a dataset almost certainly built through automated scraping pipelines pulling data from LinkedIn and other professional platforms. That is not a typo. 4.3 billion. For context, LinkedIn currently has fewer than a billion users. The researchers noted that the database contained ready-made categories for profiles, contacts, and employment history, indicating that this was an industrial-scale automated scraping and data collection operation.
This was not an isolated incident. In October 2025, LinkedIn filed a lawsuit against a software company called ProAPIs, alleging that the firm had created millions of fake LinkedIn accounts to scrape and then sell user data at rates of up to fifteen thousand US dollars per month. LinkedIn’s legal filing describes a network of fake profiles designed specifically to evade detection while harvesting names, job titles, employer information, and organisational structure data on a continuous basis.
Here is why that matters in practice. LinkedIn is unique among social media platforms because its users actively curate their professional profiles. People keep their job titles current. They list their direct managers and they detail their responsibilities. They map, in detail, exactly where they sit inside an organisation.
A threat actor who can build that picture at scale, of who reports to whom, and who handles finance, who manages access to critical systems, can craft an attack so targeted and so credible that it barely resembles a phishing email at all. It looks like an internal memo.
The Scale of the Information Already Available Online
If you work in the corporate world and have a LinkedIn profile, you should operate on the reasonable assumption that your professional information has already been scraped, compiled, and sold. SpyCloud’s 2025 Annual Identity Exposure Report found that the volume of exposed PII assets climbed by 39 % between 2023 and 2024, from 32 billion to 44.8 billion individual records. In 2024 alone, the National Public Data breach exposed 2.7 billion records, including approximately 272 million unique Social Security numbers. This equates to roughly 80% of the entire US population. Ninety-one percent of organisations reported suffering an identity-related security incident in the same year.
These numbers are not shared to cause hysteria and paralysis. We bring this awareness because understanding the landscape is the first step to changing behaviour. The reason PII matters so much in the context of social engineering is this: the more accurate the information a threat actor has about you, the more believable their attack scenario will be.
Accuracy removes suspicion. It allows the attacker to handle objections during an exchange on a call. A message that uses your manager’s name and references a real project when it arrives from inside the company’s ecosystem, and uses the specific language of your industry, no longer becomes another phishing email to move to the spam folder, to someone with a low cyber posture it is another Tuesday morning request, with a side of urgency.
The Quiz That is Not Really About You
Back to your porn star name. We use this particular social engineering tactic example because while it has been documented for years, it persists, people still take part, and it keeps working because it has evolved. The early iterations were almost comically transparent: “Your celebrity stage name is your mother’s maiden name plus the street you grew up on! Post in the comments!” A blatant attempt to harvest standard security question answers, and most people with any digital literacy saw through it.
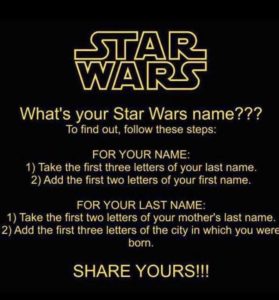
Figure 1– Example of Credential Harvesting
The modern versions are much more sophisticated and considerably less obvious. They are embedded in authentic looking graphics, circulated by friends, and designed to feel like harmless entertainment. They ask for your birth year, your first pet’s name, your childhood street, your first car, or your favourite teacher. None of these feel like security questions, yet they all are. ZeroFox security researchers have noted that these viral prompts mirror almost exactly the categories of information banks and financial institutions use for identity verification, your first pet, your childhood street, your high school mascot, repackaged as entertainment.
This is exactly how Sarah Palin’s account was breached in 2008 by a 20-year-old university student with no advanced technical skills during a US presidential election campaign. According to the hacker, it took 45minutes on Wikipedia and Google to find the information. The security question “where did you meet your spouse?” was answered by a Google search, Wasilla High School. This method is the exact same method used by Scattered Spider on MGM in 2023 15 years later, with a little more sophistication and knowledge of Yahoo’s account recovery process.
The problem is compounded when you grant quiz applications access to your social media profile. In order to retrieve your results, many of these apps request permissions to your friends list, your birthday, your email address, and your posting history. This is not a quiz, it might as well be a diary of all your valuable information.
Research published by Google security engineers found that security questions are no longer secure or reliable as standalone account recovery mechanisms anymore, exactly because of this dynamic. The answers most people choose are either easy to remember or easy to guess, and social media has made the two increasingly available publicly.
How the Pieces Become a Person
Modern threat actors do not need all the information to begin an attack. They use a process called triangulation. They take your job title from LinkedIn, your employers name from your public bio, how old you are from a quiz you took in 2022, your neighbourhood from a geographically tagged (Geotag) photo on Instagram, and your manager’s name from a conference or event where you registered a profile that you forgot existed. Individually, none of these pieces are particularly sensitive. Together, they form a picture so detailed, that it is enough to impersonate you, or to impersonate someone you trust.
This is the mechanism behind spear phishing, targeted attacks built on real personal information rather than a generic shotgun approach. Mass phishing campaigns send the same fraudulent invoice to ten thousand people in the hopes that an acceptable percentage will click on the link or image, a spear phishing attack is highly personalised. It references real details and mimics actual relationships. It arrives at a time that goes unnoticed and uses language that sounds like the person it is supposedly coming from. The difference in click rate between the two approaches is very distinct, and this is entirely down to the quality of the PII available to these attackers.
Sensitive Information is a Cybercriminal’s Treasure Chest
Beyond standard PII sits a category of information that is both more tightly regulated and more dangerous in the wrong hands. Financial records, medical and health data, biometric markers, criminal history, sexual orientation, religious beliefs, political affiliations, and genetic information. This data is especially valuable to threat actors because it enables not just fraud and identity theft, but discrimination, blackmail, and extortion. The higher the sensitivity of the information, the longer its shelf life as a tool of control.
What many people do not appreciate is that the value of their sensitive information to an attacker extends well beyond what they can steal from that individual directly. A compromised employee with access to financial systems, client records, or internal infrastructure is not just a victim. They become an entry point. Their identity, their credentials, and the trust their colleagues, place in them are the attack surface. This is why protecting PII is not purely a personal privacy concern, it is an organisational security concern, and it belongs in the same conversation as firewalls, endpoint protection, and incident response plans.
So, What do we Actually do About it?
Some of us might feel that the situation is hopeless because of the sheer scale of the problem and might succumb to the fact that our information is already out there, so we live with it. And to some extent, this is correct, but the goal is not to have perfect information hygiene in a world where much of your information has already been compromised. The goal is to reduce our attack surface, change our behaviour going forward, and make ourselves a less attractive and less lucrative target.
Take stock of your digital footprint. Does your LinkedIn profile really need to include details about your high school? Does a public audience really need to know your manager’s name, or the exact starting date, or your internal team structure? Take into account what is necessary at a professional level, versus what is criminally useful to someone building a profile targeting you, your colleagues or your company.
Stop taking the quizzes.
We are social creatures, it is in our nature to want to partake in the fun and socialise. If we use personal information in our passwords as a habit, the reality that we might be unlocking the door to our privacy will become clear when our information is used against us, or someone in our close circles who knows us. It is not worth it, using generic passwords or a password manager can be a preventative measure, but so is not easily handing over your information.
If a quiz asks for your birth year, your childhood street, your first pet, your first car, or your mother’s maiden name, the answer is a hell no! The answer should always be hell no! Finding out your porn star name is not cute, it is not relevant. Your family is, and your bank account is, and by that reasoning so is your company’s security.
Stop handing over the keys.
Have a look at your privacy and security settings and review which third-party applications have been granted access to your profile (these change regularly, so you should review this at least once a year). That quiz you took in 2019 may still have standing access to your data.
Treat your indirect information as seriously as you would treat your direct information. Your job title and data such as your geolocation are not sensitive on their own, but together with your employer, your daily schedule, and your team structure, or manager’s name, they can be a blueprint for a devastating attack. Think about what the combination of your publicly available information reveals as a whole.
Enable multi-factor authentication everywhere if it is available to you. If a threat actor does manage to obtain your credentials or correctly answer your security questions, MFA is often the final barrier between your account remaining secure and your identity becoming someone else’s property.
We are Part of the Problem, but We are Not to Blame
There is a phrase that is often cited by professionals and writers in the cybersecurity space that people are the weakest link in the system. Part of this is true. We operate in a systematic environment built of networks and social platforms that scream for our information or exclude us from participating in “the Fun”. Apps and websites are designed to extract information from us like parasites extract our blood, often unseen and unheard until it is much too late. The internet machine is geared towards the extraction of our identity, mostly for our benefit and convenience, often for malevolent means.
This does not absolve us from our individual responsibility of guarding information, ours and others by default. It does make one thing agonisingly clear, those who refuse to hand over their most valuable data without question, who read the fine print, decline the cookies, provide anonymous details, and don’t fill in every form put in front of them, are doing something most people won’t. They are pushing back, and in a world that profits from passive compliance and data extraction, that’s not a small thing.
References
SpyCloud. (2025). SpyCloud Annual Identity Exposure Report 2025. https://spycloud.com/resource/report/spycloud-annual-identity-exposure-report-2025/
Cybernews. (2025, December 12). Major leak reveals one of the largest lead-gen databases ever exposed. https://cybernews.com/security/database-exposes-billions-records-linkedin-data/
Security Affairs. (2025, October 6). LinkedIn sues ProAPIs for $15K/Month LinkedIn data scraping scheme. https://securityaffairs.com/183001/security/linkedin-sues-proapis-for-15k-month-linkedin-data-scraping-scheme.html
The Record / Recorded Future News. (2025, October 3). LinkedIn sues software company allegedly scraping data from millions of profiles. https://therecord.media/linkedin-sues-data-scraping-company
Trend Micro. (2022). A Growing Goldmine: Your LinkedIn Data Abused for Cybercrime. https://www.trendmicro.com/vinfo/us/security/news/cybercrime-and-digital-threats/a-growing-goldmine-your-linkedin-data-abused-for-cybercrime
ZeroFox. (2024, March 18). How Hackers Use Social Engineering to Get Passwords on Facebook. https://www.zerofox.com/blog/innocuous-facebook-quizzes-attacker-intel-goldmines/
CNP Technologies. (2025, March 28). The Hidden Dangers of Social Media Quizzes. https://www.cnp.net/the-hidden-dangers-of-social-media-quizzes/
Silicon Canals. (2026, February 5). Why your social media quiz answers are being harvested and the security questions they’re stealing. https://siliconcanals.com/a-bt-why-your-social-media-quiz-answers-are-being-harvested-and-the-security-questions-theyre-stealing/
Huntress. LinkedIn Data Breach: What Happened, Impact, and Lessons. https://www.huntress.com/threat-library/data-breach/linkedin-data-breach
Basil Polydorou – Head of Learning Solutions | BsC Cyber Psychology Candidate